The Role of CMMC in Reshaping the Industry’s Cybersecurity Approaches
In this era of digital acceleration, manufacturing firms are leveraging modern technologies to augment efficiency, cut down expenses, and retain […]

Five Key Strategies for Cybersecurity in Law Firms Embracing Remote Work
In the modern age where remote work is the new normal, legal practices face a distinct set of hurdles. Beyond […]

Choosing the Right IT Service Provider for Your Law Firm: A Comprehensive Guide
Today’s legal businesses rely heavily on IT to stay competitive in the modern corporate landscape. Legal practices rely heavily on […]
Navigating Regulatory Compliance in the Legal Industry
Opportunities and challenges abound in today’s globally networked legal industry. One of the most significant problems is the complex regulatory […]

Strengthening Law Firms: The Key Role of Employee Cybersecurity Training
In today’s digital environment, with the increasing sophistication of cyber attacks, it is crucial for law firms to take precautions […]

Unleashing the Potential of Cloud Computing for Law Firms
In today’s rapidly transforming digital era, businesses across sectors are leveraging cutting-edge technologies to improve their services and meet the […]

The Network Pro: Powering IT with Humanity and Excellence
Welcome to the vibrant world of The Network Pro! We are a guiding beacon of innovation and customer service excellence […]

The Importance of Having a Contingency Plan for Your Law Firm
Natural catastrophes and cyber attacks are two examples of the kinds of events that can strike with little or no […]

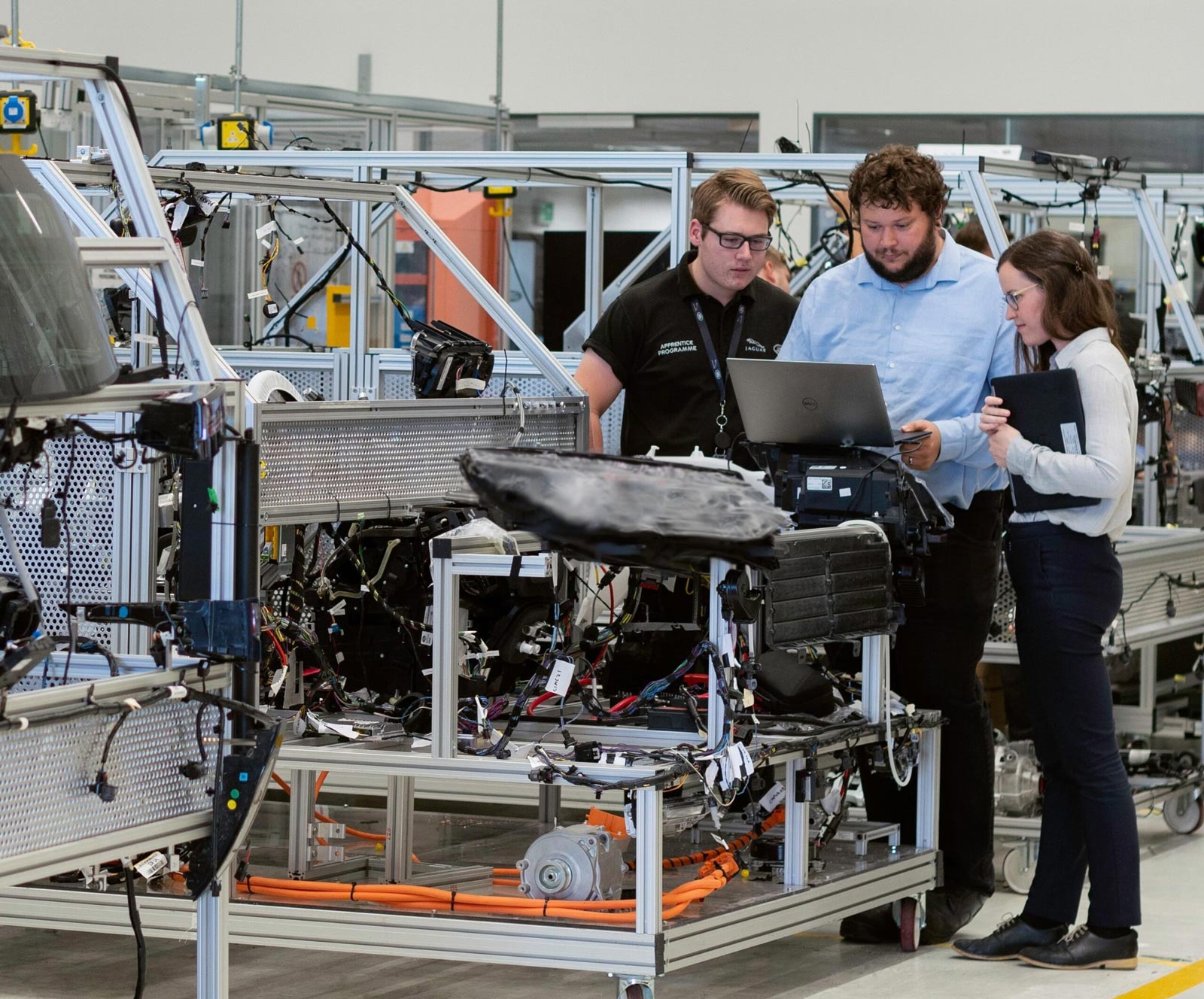
The Critical Function of the CMMC Framework in Manufacturing
Safeguarding sensitive information, protecting intellectual property, and ensuring the integrity of operations is crucial as the manufacturing industry becomes more […]

Top 3 Cybersecurity Risks for Law Firms in 2023 and How to Mitigate Them
As more and more legal practices move their operations online, they become increasingly vulnerable to cyberattacks. Since cybercriminals are always […]

The Critical Functions of Cloud Computing and Cybersecurity in Protecting the Legal Sector
The legal industry is always developing, and in the modern digital age, cloud computing has become a revolutionary resource for […]

Cloud Computing: What Are The Cybersecurity Risks?
Whether you are considering cloud computing for personal use or you want to use it for business operations, these are […]

Data Protection: Strong Internal Defense For Better Protection
There is no doubt about the fact that digital security is a growing concern for both private users as well […]

